|
Often we are asked to help our customers with fraud issues - sometimes in that proactive situation..... sometimes the ambulance at the bottom of the cliff hunting back through transactions for evidence for prosecution. As a company grows, often your are required to introduce audit controls by your board or shareholders. This approach can be viewed as the "annual challenge" to see how quickly you can get the auditors out of your hair, or it can be looked upon proactively as and opportunity to demonstrate how well you have your house in order. Having worked through many systems and procedure audits at central and local government plus in highly accountable private organisations we have seen a lot of different methods for review of how these organisations are keeping on top of potential employee fraud. Many do not have regular checks other than the annual audit and many do not have push/exception based notification of any breaches of policies. Often what is audited (when you're forced to be audited) are the simple things, like password policies, large transactions getting appropriate evidenced approvals etc. What is often overlooked are things like.: - discounting - excessive supply ordering for kickbacks or pocketing excess stock - stock write offs / stock counting - new supplier agreements (suppliers are often keen to woo new customers with some freebies) - ANYTHING where cash is handled - changes in payment terms - updates to supplier bank accounts - who can issue credits? - access to prepaid postage or courier packs - who locks up the premises? In the D!gitalist Magazine, they suggest that one of the key risk areas is Supplier/Employee relationships. (Read it here). With significant fraud it may be a lone employee or even an owner, however its also common to see groups of employees developing "its ok to take one...", or "they've got plenty.." attitudes. Each one of these transactions that is not disclosed is hurting your business.... and do you really know what the volume or value of these non-disclosed transactions is? The figures in the article suggest lone employees will do damage, but often collusion of multiple employees - maybe just skimming - is really hurting business. There are a mountain of things you can track and attempt to monitor. Maybe you're ok because you'd know if you were loosing a lot? But what is the cost of the skimming that's being done? $10...$100's.... $1000's or more? over how many years..? But how do you get your organisation in order..... (and actually keep running the business)? There are some basic starting points...... Cash, credit and payments are great places to get basic controls in place. Build up what you are auditing, with the most critical areas first and develop the full audit scope over time. #1 Get the AS-IS Visible First look at what is currently done, by whom and get those processes written down - even get your employees to write it down - its a great learning opportunity and will save you consulting time if you have something to work from. (We can also provide templates so your processes can be documented in a standardized way). #2 Decide the To-Be Then seek expertise from several sources - your accountants/auditors AND us! For each process there will be multiple auditable areas - some of these will rely on non-system policies (eg. what customers can get the Gold Price List? ) but the decisions made outside any system are often recorded IN your systems - so look at what guidelines or policies employees need to make the right decisions and then lets establish the best method for tracking this adherence to policy. Some measures you implement will allow you to stop or prevent fraudulent activity, however many organisations - in particular small organisations rely on few people to do many activities. This is where you will need to implement Detective measures using Alerts/Notifications, Reports and even random audits of transactions. #3 Publicise Publicise Publicise Many organisations are keen to track and monitor KPIs and readily report on these at management/board levels - however you need to get your audit measures here also so you can say "hey look, sales are up this month..... AND we know we aren't losing money through the back door too...!" Then take those measures down to each level in the organisation and share them.
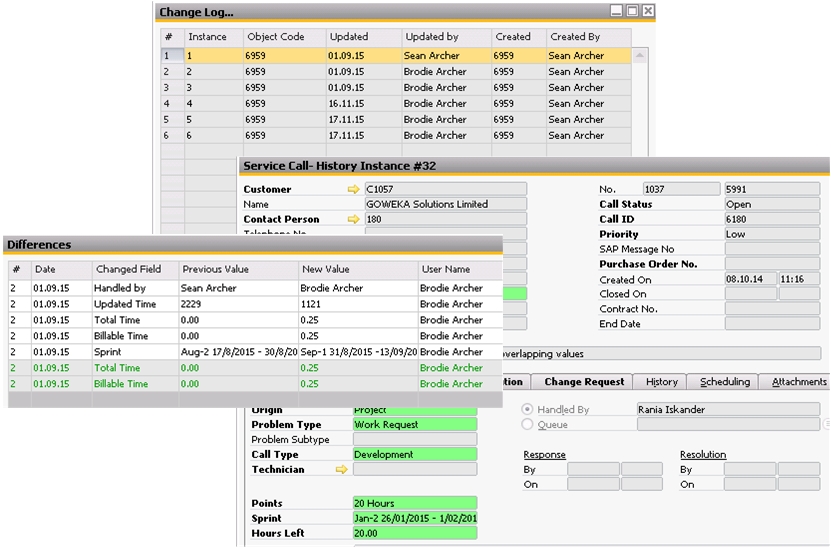
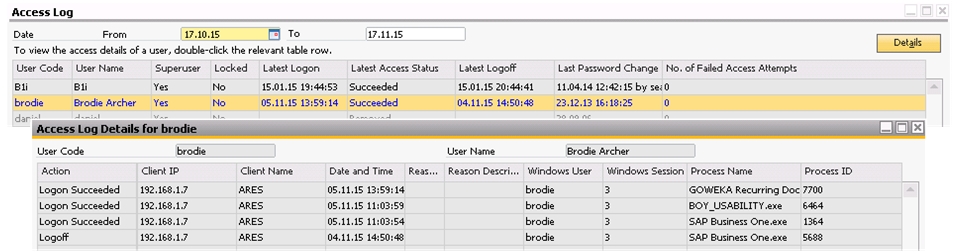
The more risky transactions are shared, talked about in meetings and monitored, the less likely you are to have issues with employees thinking no one is watching. Native Tracking in SAP Business One SAP Business One on its own tracks who, what and when transactions are created or updated, when the system has been accessed and gives you tools like the Alerts and Approval Procedures to track items specific to your business. Licensing and Authorizations are your first line of defense, deciding who can do what is one of the critical steps in securing your organisation from fraud attempts. These Preventative measures help endorse who can do what in your organisation. With SAP Business One we use Approvals and Alerts a lot as detective measures where you need to allow users to complete certain transactions (eg. allow discounting, create credits) but you want to know when and how often they are stepping too close to the mark. With both Approvals and Alerts we can target these to specific scenarios that are relevant to your users and your business - meaning you are are only notified when those conditions occur, as you learn more about their use of the system, the alert limits can be updated as your business changes. There are some simple tools all users can use within SAP Business One - whether to track mistakes or if they suspect something is up with the data they are working with. The Change and Access logs are easy options for users to become familiar with and are normally included in Basic Navigation training. The Change Log This is easliy viewed via the System Menu > Tools > Change Log... Within here you can see a simple summary of who updated the records, using Show Differences you can see what specific fields were updated and their values, then Double-Clicking an entry in the Change Log form opens a Read-Only version of the document as it was, allowing a more familiar way to view any updates. Under the System Menu > Tools > Access Log... you have visibility of when users last logged in/off, last password changes and unsuccessful logon attempts. Double-Clicking a user allows you to see other connection information, like what add-ons were started, windows user for the session and IP addresses. You can change dates to see information for any day. Contact Brodie at Business Evolution Group to discuss where you are currently at and let us see how we can help you develop good practice in this area.
0 Comments
Your comment will be posted after it is approved.
Leave a Reply. |
Categories
All
Archives
April 2017
AuthorBrodie Archer is the Principal Consultant at Business Evolution Group. Contact.
|



 RSS Feed
RSS Feed